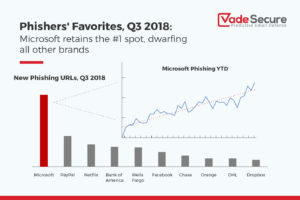
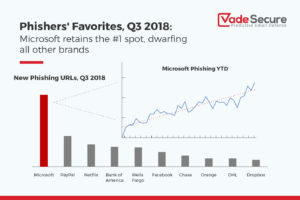
A new phishing report has been released that keeps track of the top 25 brands targeted by bad actors. Of these brands, Microsoft, Paypal, and Netflix are the top brands impersonated by phishing attacks.
Email security provider Vade Secure tracks the 25 most spoofed brands in North America that are impersonated in phishing attacks. In their Q3 2018 report, a total of 86 brands are tracked, which consist of 95% of all attacks detected by the company.
Overall, Vade Secure has stated that phishing attacks increased by 20.4% in the 3rd quarter with the most targeted being Microsoft, followed by PayPal, Netflix, Bank of America, and Wells Fargo.

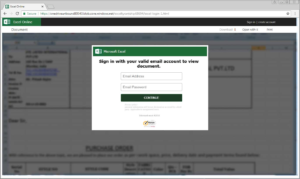
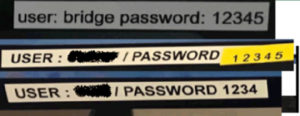
Cloud based services and financial companies remain the two most targeted industries with Microsoft being the top targeted brand as attackers try to gain access to Office 365, One Drive, and Azure credentials.
“The primary goal of Microsoft phishing attacks is to harvest Office 365 credentials,”stated Vade Secure’s report. “With a single set of credentials, hackers can gain access to a treasure trove of confidential files, data, and contacts stored in Office 365 apps, such as SharePoint, OneDrive, Skype, Excel, CRM, etc. Moreover, hackers can use these compromised Office 365 accounts to launch additional attacks, including spear phishing, malware, and, increasingly, insider attacks targeting other users within the same organization.”
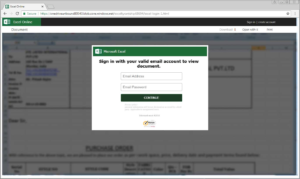
Office 365 phishing emails typically indicate that the recipient’s account has been suspended or disabled and then prompts them to login to resolve the issue. These phishing forms are almost identical to a legitimate Office 365, and by creating a sense of urgency, the attackers hope the victims will be less vigilant as they enter their credentials.

Followed by Microsoft, are PayPal phishing schemes where attackers try to gain access to victim’s money and Netflix, which is used to steal credit card information.
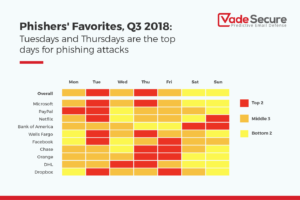
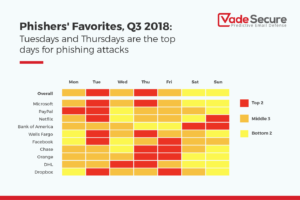
Of particular interest is that attackers tend to follow a pattern as to what days they send the most volume of phishing emails. According to the report, most work related attacks tend to occur during the week with Tuesday and Thursday being the largest volume days. For Netflix, the most targeted days are Sunday when people are taking a break to watch some TV.
Phishing attacks become more targeted
Vade Secure has also noticed that attackers are starting to decrease the amount of times a particular URL is used in a phishing campaign. Instead attackers are using unique URLs in each phishing email in order to bypass mail filters.
“What should be more concerning to security professionals is that phishing attacks are becoming more targeted,” continued Vade Secure’s report. “When we correlated the number of phishing URLs against the number of phishing emails blocked by our filter engine, we found that the number of emails sent per URL dropped more than 64% in Q3. This suggests that hackers are using each URL in fewer emails in order to avoid by reputation-based security defenses. In fact, we’ve seen sophisticated phishing attacks where each email contains a unique URL, essentially guaranteeing that they will bypass traditional email security tools.”
Protecting yourself from phishing attacks
As phishing attacks become more sophisticated, they also become harder to detect. Using cloud services, attackers are now able to secure their phishing forms with SSL certificates from well known and trusted companies such as Microsoft and Cloudflare. This allows the forms to look authentic to victims.
As you can see from phishing attack below, the login form looks legitimate, the site is on a Microsoft owned domain, and the page is secured. To many, this would appear as a legitimate Microsoft form. In reality, the attacker is hosting their form on a Microsoft cloud service in order to create this sense of legitimacy.
Therefore, it is always important to scrutinize a site before entering any login credentials. If the URL looks strange, there is incorrect spelling, grammar is incorrect, or something does not feel right then you should not enter any account credentials. Instead contact your administrator or the company itself if you are concerned your account has problems. If you don’t know the sender, don’t open the email.