PETYA RANSOMWARE
The latest sweeping ransomware assault bares some similarity to the WannaCry crisis that struck seven weeks ago. Both spread quickly, and both hit high-profile targets like large multinational companies and critical infrastructure providers. But while WannaCry’s many design flaws caused it to flame out after a few days, this latest ransomware threat doesn’t make the same mistakes.
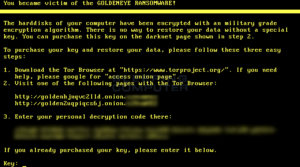
Originally identified as Petya, a ransomware that first started circulating in 2016, the current attack now appears to be a Petya offshoot, with added refinements such as stronger encryption. Some researchers call this new iteration “NotPetya” or “GoldenEye,” while others still refer to it as Petya. Regardless of the name, it has already hit 2,000 targets, seizing the systems of high-profile victims like Danish shipping giant Maersk, US pharmaceutical company Merck, and multiple private and public institutions in Ukraine.
And while it owes its rapid spread in part to EternalBlue, the same stolen NSA exploit WannaCry leveraged, it lacks several of the traits that made WannaCry—which turned out to be an unfinished North Korean project gone awry—easier to stop.
WannaBreak
“The quality of the code improves from iteration to iteration—this GoldenEye ransomware is pretty solid,” says Bogdan Botezatu, a researcher at the security firm Bitdefender. “We don’t get to catch a break.”
The most important WannaCry pitfall that this current round sidesteps? A kill switch that allowed researchers to neuter the ransomware around the world and drastically reduce the spread. The mechanism was a low-quality, possibly unfinished feature meant to help the ransomware avoid analysis. It backfired spectacularly. So far, GoldenEye shows no signs of containing such a glaring error.
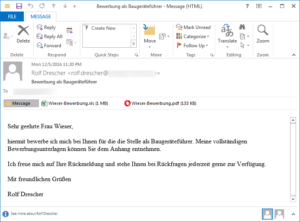
Additionally, WannaCry spread between networks across the internet like a worm, relying almost entirely on EternalBlue to get in and hitting systems that hadn’t yet downloaded Microsoft’s patch for that vulnerability. This new ransomware also targets devices that somehow still aren’t secured against EternalBlue, but can deploy other infection options as well. For example, the attackers seem to be spreading the ransomware through the software update feature of a Ukrainian program called MeDoc, and possibly through Microsoft Word documents laced with malicious macros.
Along with exploiting EternalBlue to gain access when possible, the ransomware can also leverage an additional Shadow Brokers-leaked NSA exploit known as EternalRomance (patched by Microsoft in March) for remote access. And some researchers have also found unconfirmed evidence that the ransomware may take advantage of yet another tool published by the ShadowBrokers, known as EsteemAudit, that specifically targets computers running Windows XP and Windows Server 2003. Microsoft patched that vulnerability two weeks ago as part of its unprecedented effort to secure its old, unsupported operating systems against leaked NSA exploits.
Once inside the network, the ransomware steals administrative credentials, giving it control over powerful system management tools like Windows PsExec and Windows Management Instrumentation.
“If a system with enough administrative privileges is compromised, it will simply instruct all other PCs it has access to run the malware as well,” says Fabian Wosar, a security researcher at the defense firm Emsisoft, which specializes in malware and ransomware. “That is why a lot of system administrators are freaking out right now.”
Smarts, Not Scale
Because GoldenEye appears to take a more targeted approach to infection, rather than barreling around the internet, it has so far resulted in fewer infections: it has affected 2,000 targets versus the hundreds of thousands that WannaCry hit. But don’t read that as a weakness necessarily. WannaCry’s ability to spread over the internet led to out-of-control infections, and its creators were ill-equipped to handle that volume of potential payments.
In fact, WannaCry hackers proved incapable of tracking payments whatsoever. Attackers had victims send ransoms to one of four set bitcoin addresses, instead of assigning each target a unique address. This made incoming payments difficult to track, and left it to the criminals to figure out which victims (among hundreds of thousands) had paid and should be sent a decryption key.
Payment happens to be GoldenEye’s current weakness as well, though not due to WannaCry-level incompetence. It relies on manual payment validation, meaning that when victims pay the ransom they must email proof of payment to an email address, after which hackers send a decryption key. Not only does a manual system make it harder for attackers to get paid, it can reduce victim faith that paying the ransom will result in decryption.
Also? The hackers’ email provider, Posteo, pulled the plug on their account, making payment confirmation pretty much impossible.
No Easy Fix
This latest round of ransomware appears to be here to stay. The diversity of delivery options means that no single patch can necessarily provide complete protection against it. Still, administrators can take some steps to protect their systems. Analysts agree that while patches don’t solve everything in this situation, they are still crucially important and do offer real defense. “Very, very important to patch,” says MalwareHunter, a researcher with the MalwareHunterTeam analysis group.
Researchers also note that the ransomware runs on boot, meaning that if you can disrupt a system before Windows boots, or if you encounter a “Check Disk” message, you can avoid having your files encrypted by quickly powering down.
Additionally, for the current variant of ransomware, administrators can stop the spread within a network from the Windows Management Instrumentation by blocking the file C:\Windows\perfc.dat from running.
“The problem is, patching is only one method of defense,” says David Kennedy, CEO of threat detection firm Binary Defense. “Credential harvesting and using that for lateral movement was the big impact in this situation.”
All of which provides cold comfort for those already impacted. And based on how many companies ignored the EternalBlue patch, even after the WannaCry threat, it may not end up slowing down the current outbreak at all.
First place to start make sure your systems have the latest patches and updates !!!