
There’s an easy way to protect your data in the cloud.
As Apple continues to resist FBI demands to unlock a terrorist suspect’s phone, it raises a question: What if Amazon Web Services was ordered to provide access to a customer’s cloud? Would AWS hand the data over to the feds?
+MORE AT NETWORK WORLD: Tim Cook issues internal memo on ongoing FBI/iPhone saga | VMware turns to IBM in the public cloud +
Amazon’s terms of service provide us a clue. AWS says it complies with legally binding orders when compelled to do so. Here’s a statement from Amazon’s FAQ on cloud data privacy (which is not written specifically about the Apple-FBI issue):
“We do not disclose customer content unless we’re required to do so to comply with the law or a valid and binding order of a governmental or regulatory body. Governmental and regulatory bodies need to follow the applicable legal process to obtain valid and binding orders, and we review all orders and object to overbroad or otherwise inappropriate ones.”
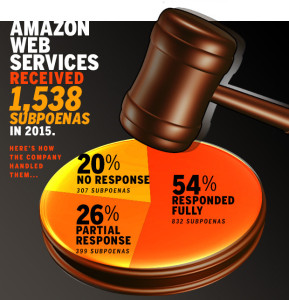
Most of the time, when ordered to hand over data, Amazon does so. In 2015 AWS received 1,538 subpoenas from law enforcement officials, according to information the company recently began making public. Just over half the time (in 832 cases, or 54% of the time) AWS complied fully with those orders. Another quarter of the time (in 399 cases) Amazon partially responded to the request for information, while in the remaining 20% of cases AWS did not respond to the subpoena.
For customers who are concerned about Amazon handing over their data to the government, there are protections that can be put in place. “There’s a huge market focused on encrypting data stored in the cloud, and giving the customers the keys,” explains 451 Research analyst Adrian Sanabria. If customers use a third-party encryption service to scramble their data and manage the keys themselves, then even if Amazon did hand over the data to the feds, it would be useless. “Yes, it does sometimes create some issues with flexibility and breaking functionality, but it is there as an option if you want it, and (if done properly) AWS (or the government) can’t decrypt the data,” Sanabria says.
+ MORE ON APPLE: Apple and the FBI will need to compromise, Cisco’s CEO says +
AWS offers multiple different encryption methods, including ones that are built in automatically to some services – like S3, the Simple Storage Service, and others that customers manage themselves, such as the Hardware Security Module (HSM). AWS’s marketplace offers a variety of additional encryption and security services from independent software vendors.
Amazon says that it notifies customers when there’s been a request for their data to be handed over, unless there’s a compelling reason not to do that; for example if its clear the cloud service is being used for an illegal purpose.
AWS is more stringent about not providing other types of information to the government. In the second half of 2015 alone, AWS received 249 “National security requests” but did not comply with any of them. AWS also received 78 requests from non-U.S. entities, the vast majority of which (60) the company did not respond to.
AWS did not respond to a request to comment on this story.
Microsoft Azure basically has the same policy, according to the company’s website, saying “We do not provide any government with direct or unfettered access to your data except as you direct or where required by law.”
Even with all the concern over providers or the government being able to access data, Sanabria estimates that only a minority of cloud users encrypt data and manage their own keys.

One response to “If Amazon were in Apple’s position, would it unlock its cloud for the feds?”